HashiCorp Launches Vault Radar to Enhance Secret Management
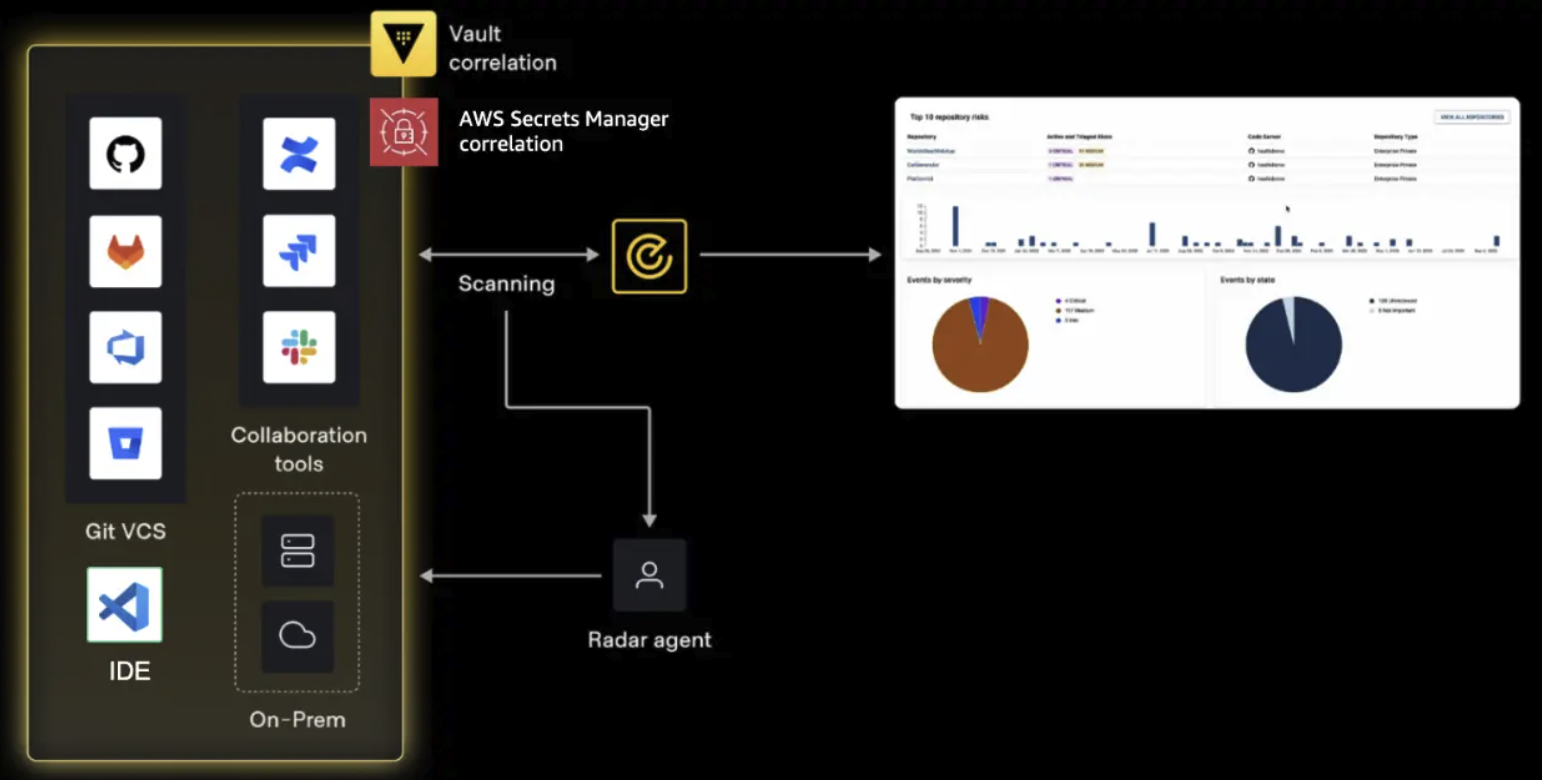
HashiCorp has introduced Vault Radar, a tool designed to streamline the detection and remediation of exposed secrets across code repositories, collaboration tools, and cloud environments. Launched recently, Vault Radar aims to not only identify security vulnerabilities but also to facilitate a more mature remediation process that emphasizes accountability and measurable progress in managing sensitive information.
Improving Secret Detection with Correlation
Effective secret management begins with understanding the context of detected vulnerabilities. Vault Radar enhances this process by correlating findings with existing secrets stored in systems like HashiCorp’s Vault and AWS Secrets Manager. This correlation allows teams to quickly discern whether a detected secret is unmanaged or already under centralized control.
This added context transforms each finding into actionable insights. For instance, if a secret is identified as already managed in Vault, teams can address it with a clearer understanding of its ownership and lifecycle management. Conversely, if a secret is uncorrelated, it may indicate that credentials are being mishandled outside approved workflows. Such distinctions are crucial for determining the appropriate remediation path.
Over time, this correlation capability provides valuable insights into organizational practices surrounding secret management. By identifying patterns of compliance or non-compliance across teams, organizations can better prioritize their remediation efforts and strengthen governance over their sensitive data.
Integrating Webhooks for Seamless Remediation
A key aspect of effective secret remediation is ensuring that exposure notifications reach the right stakeholders promptly. In many organizations, the remediation process spans multiple tools and platforms, including ticketing systems and messaging applications. Vault Radar addresses this challenge by incorporating webhook support that allows real-time event data to be sent to external systems.
This integration facilitates smoother transitions from detection to action by automatically routing findings to relevant teams or triggering follow-up processes. For example, it can automatically create tickets in project management tools or send alerts through collaboration platforms. By embedding secret remediation into existing operational workflows, organizations can reduce friction between discovery and response efforts.
The ability to connect findings directly with the tools teams already use not only streamlines the remediation process but also enhances scalability and coordination across departments. This integration ensures that organizations can respond effectively to security threats without disrupting established workflows.
Enhanced Visibility Through Remediation Reporting
As organizations implement secret detection programs, visibility into both findings and progress becomes essential. Remediation reporting offers a comprehensive view of how well an organization is managing its exposure risks. It tracks metrics such as new versus resolved secrets and the timelines associated with remediation efforts.
This level of visibility shifts the focus from merely counting detected secrets to evaluating how effectively organizations are reducing exposure over time. By analyzing trends in open versus resolved issues, teams can prioritize their efforts more confidently while identifying areas where response times may be lagging.
For security leaders, this reporting provides critical insights into program efficacy and highlights potential bottlenecks in the remediation process. As programs scale up, maintaining visibility becomes increasingly important for demonstrating accountability and illustrating how secret detection contributes to overall risk reduction.
Traceability: Building Accountability Across Teams
Traceability is another vital component of effective secret remediation. By maintaining a detailed lifecycle history for each detected secret—from discovery through resolution—Vault Radar enables teams to monitor progress comprehensively. This historical context allows stakeholders across security, development, and operations teams to collaborate more effectively by providing a shared understanding of ownership and status changes throughout the remediation journey.
This level of transparency not only aids in managing ongoing remediation efforts but also supports compliance audits by documenting how incidents were handled over time. Such records allow organizations to review actions taken during security events thoroughly and ensure adherence to established processes.
As secret detection programs grow more complex, having access to this lifecycle history becomes invaluable for identifying recurring issues or improving consistency across various teams and environments. Instead of relying on fragmented information scattered across multiple systems, stakeholders gain a cohesive view of each incident’s handling and resolution path.
From Detection to Measurable Security Outcomes
The introduction of Vault Radar marks a significant advancement in how organizations approach secret management. While detecting exposed secrets is crucial, the true measure of success lies in an organization’s ability to act on these findings effectively. Vault Radar connects detection capabilities with operational workflows through webhooks while enhancing visibility via reporting and traceability features.
This comprehensive approach fosters better coordination among teams, clarifies accountability roles, and enables measurable progress over time in reducing exposure risks associated with sensitive information.
What This Means for Organizations
The launch of Vault Radar represents a strategic move towards enhancing security posture through improved secret management practices. By facilitating better detection-to-remediation workflows and providing actionable insights into exposure risks, organizations can significantly mitigate vulnerabilities associated with sensitive data handling. The tool’s emphasis on integration with existing workflows ensures that security measures align seamlessly with operational processes—ultimately leading to stronger governance over critical assets.
For more information, read the original report here.