HashiCorp Vault Enhances SSH Access Management with Boundary Integration
HashiCorp has announced an update to its approach for managing SSH access using HashiCorp Vault, introducing integration with HashiCorp Boundary for passwordless access through just-in-time (JIT) SSH credentials. This update comes at a crucial time as enterprises increasingly adopt hybrid and multi-cloud architectures, necessitating a more secure and streamlined method for managing administrative access to Unix-like servers.
The Need for Improved SSH Access Management
SSH (Secure Shell) remains the standard connectivity method for secure administrative access to servers, but it is not without its challenges. Key management risks have prompted organizations to seek solutions beyond traditional SSH key management tools, which often only address symptoms of a larger issue: effective secrets management. With the latest updates from HashiCorp Vault, a more robust architecture is now available that simplifies SSH access while ensuring security across both on-premises and cloud environments.
Key Updates in HashiCorp Vault 1.13+
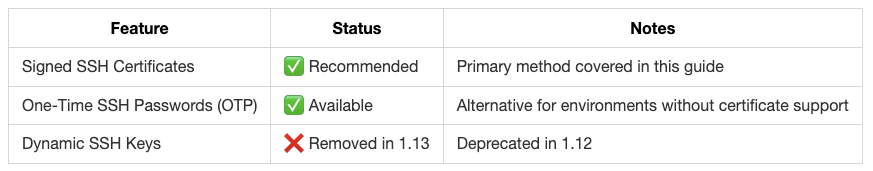
The latest version of HashiCorp Vault introduces several significant changes aimed at enhancing SSH access management:
The dynamic SSH keys feature has been removed in favor of a recommended approach that utilizes signed SSH certificates.
A new integration section has been added that covers JIT credential injection through Boundary, allowing users to achieve seamless passwordless SSH access.
Best practices have been refined to align with modern Vault deployments, ensuring optimal performance and security.
Understanding the Risks of Traditional SSH Key-Based Authentication
Traditional SSH key-based authentication presents several risks:
The potential compromise of private keys due to mishandling by users can lead to unauthorized access.
Key rotation can be complex; revoking private keys requires thorough tracking and management, especially when personnel changes occur.
A lack of inventory tracking for keys increases the risk of unauthorized access as numerous keys accumulate over time.
Managing keys consistently across multiple systems and environments adds complexity and heightens the risk of incidents related to mismanagement.
A Secure Alternative: SSH Certificate Authentication
To address these challenges, organizations are increasingly turning to SSH certificate authentication. This method operates similarly to SSL certificates, where public keys are signed by a trusted certificate authority (CA). Key benefits include:
Automatic expiration of signed certificates ensures that once they expire, they can no longer be used for connections.
Only valid certificates signed by the trusted CA’s private key will be accepted, enhancing security.
Instructions can be embedded during signing, such as specifying valid usernames or disabling port forwarding.
The Workflow for Using HashiCorp Vault with SSH Certificates
The workflow for implementing this architecture involves several steps:
- User creates a personal SSH key pair.
- User authenticates to Vault using their identity provider credentials.
- User submits their public key to Vault for signing.
- Vault signs the public key and returns a signed SSH certificate.
- User initiates an SSH connection using the signed certificate.
- The target host verifies the certificate against the trusted CA and allows connection if valid.
User Requirements and Role-Based Access Control
This architecture allows organizations to implement role-based access control (RBAC) through Vault policies. Each user is assigned specific roles that dictate which certificates they can sign based on their function within the organization. This ensures that users only have access to what they need, reducing potential security risks associated with over-privileged accounts.
Integrating Boundary for Passwordless Access
The integration of HashiCorp Boundary with Vault takes this architecture further by enabling passwordless access through credential injection. Boundary serves as a modern privileged access management solution designed specifically for cloud environments. It facilitates:
- User authentication through trusted identity providers like Okta or Azure AD.
- Authorization based on defined roles and services.
- A seamless connection to dynamic infrastructure without exposing sensitive credentials.
- Session recording capabilities for compliance and auditing purposes.
The Synergy Between Vault and Boundary
This integration offers a complete just-in-time (JIT) solution for managing SSH access at scale. The process involves:
- User authenticates via Boundary using corporate identity credentials.
- User requests access to an SSH target managed by Boundary.
- Boundary retrieves necessary credentials from Vault’s SSH secrets engine on behalf of the user.
- If brokered credentials are used, Vault signs the user’s key; if injected credentials are employed (Enterprise feature), they are automatically injected into the session without user visibility.
Why This Matters
The enhancements in HashiCorp Vault’s approach to managing SSH access reflect an urgent need in today’s digital landscape where security threats are ever-present. By adopting this updated architecture featuring integrated solutions like Boundary, organizations can achieve centralized control over their infrastructure while minimizing risks associated with traditional key management methods. The result is a streamlined process that not only secures administrative access but also enhances operational efficiency across diverse cloud environments. As enterprises continue their digital transformation journeys, leveraging such advanced tools will be crucial in safeguarding sensitive data and maintaining compliance across all platforms.
For more information, read the original report here.