Trivy and KICS Address Supply Chain Attacks in 2026
In a significant development in cybersecurity, the Trivy and KICS teams recently discovered a malicious image on Docker Hub that targeted their systems. This incident, which occurred in April 2026, highlights the growing threat of supply chain attacks and underscores the importance of collaborative responses among security teams to mitigate these risks.
The Incident: A Closer Look
The malicious image was found within the Checkmarx/KICS (Kubernetes Infrastructure Configuration Scanning) repository on Docker Hub. Upon detection, immediate action was taken to quarantine the image, preventing any potential harm to users who might have inadvertently downloaded it. The swift response involved coordination between multiple security entities, including Socket and Checkmarx, showcasing the necessity for teamwork in addressing cyber threats.
This incident is part of a broader trend where attackers are increasingly targeting software supply chains. By embedding malicious code into widely used images or libraries, they can exploit vulnerabilities in applications that rely on these components. The rapid proliferation of such attacks has prompted security experts to advocate for more robust defenses and collaborative strategies among organizations.
The Role of Open Collaboration
The response to this incident emphasizes the critical role of open collaboration in cybersecurity. In an environment where threats evolve quickly, sharing information about vulnerabilities and attack vectors can significantly enhance an organization’s ability to defend against potential breaches. The Trivy and KICS teams exemplified this principle by working closely with other security professionals to analyze the threat and formulate a response plan.
Collaboration extends beyond just incident response; it involves continuous communication about best practices, threat intelligence, and emerging vulnerabilities. By fostering a culture of openness, organizations can better prepare for future attacks and create a more resilient software ecosystem.
Implications for Software Supply Chains
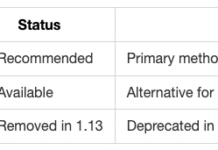
This incident serves as a wake-up call for developers and organizations that rely on third-party software components. As supply chain attacks become more sophisticated, it is imperative for companies to implement rigorous security measures throughout their development processes. This includes regular scanning for vulnerabilities in dependencies, employing automated tools like Trivy to identify issues early in the development cycle, and maintaining up-to-date knowledge about potential threats.
Furthermore, organizations should consider adopting secure coding practices and conducting thorough audits of their software supply chains. These steps not only protect against current threats but also build a foundation for long-term security resilience.
Looking Ahead: Strategies for Prevention
The ongoing evolution of cyber threats necessitates proactive strategies to safeguard software supply chains. Organizations should prioritize the following measures:
- Regular Vulnerability Scanning: Utilize tools like Trivy to continuously monitor dependencies for known vulnerabilities.
- Implement Security Best Practices: Adopt secure coding guidelines and conduct regular code reviews to minimize risks.
- Enhance Incident Response Plans: Develop comprehensive plans that include collaboration with external security teams to ensure rapid responses to incidents.
- Educate Teams: Provide ongoing training for developers and IT staff on emerging threats and best practices in cybersecurity.
- Cultivate Partnerships: Engage with other organizations within the industry to share insights and strategies regarding threat detection and response.
What This Means
The discovery of a malicious image on Docker Hub serves as a stark reminder of the vulnerabilities present within software supply chains. As attackers become more adept at exploiting these weaknesses, organizations must prioritize collaboration and proactive security measures. By fostering an environment of open communication among security teams and implementing robust defense strategies, businesses can significantly reduce their risk exposure in an increasingly hostile cyber landscape.
For more information, read the original report here.