HashiCorp Vault Expands PKI Capabilities with Public CA Integration
HashiCorp has announced a significant enhancement to Vault Enterprise’s capabilities, allowing organizations to integrate and manage public certificate authorities (CAs) directly within the Vault ecosystem. This update aims to streamline the management of X.509 certificates, addressing the challenges posed by fragmented processes that often lead to security vulnerabilities. The new feature is expected to simplify workflows for enterprises by providing a unified approach to both internal and external certificate management.
The Challenges of Fragmented Certificate Management
Organizations have increasingly turned to HashiCorp Vault for automating their internal private key infrastructure (PKI). However, when it comes to obtaining certificates that are trusted by external browsers or public networks, the automation process typically falters. This dual-track management creates several critical pain points:
- Operational Overhead: Without native integration for public CAs, teams must manually request, renew, and revoke certificates through external portals, significantly increasing the likelihood of human error and missed renewals.
- The “Outage Clock”: Manual management leads to a lack of visibility regarding expiration dates across various providers. This can result in unexpected downtime when a public-facing API or website certificate expires.
- Siloed Governance: Organizations often find themselves managing private and public certificates using different tools, complicating efforts to enforce consistent security policies and maintain comprehensive audit trails necessary for compliance with standards like NIST and PCI DSS.
- Limited External Utility: While private CAs serve well for internal trust, they fall short for customer-facing services. This reliance on disparate tools restricts Vault’s utility in hybrid and multi-cloud environments where external trust is essential.
A Unified Solution for Certificate Management
The newly introduced public CA integration addresses these challenges by centralizing the entire certificate lifecycle within Vault. Acting as a central proxy, Vault securely manages upstream CA credentials while orchestrating the complex validation processes required for public certificate issuance.
This integration allows development teams to request publicly trusted certificates using the same APIs and workflows already in place for private certificates. Consequently, organizations can achieve a centralized and automated approach that eliminates manual silos, offering a comprehensive view of their entire certificate landscape.
How Public CA Integration Works
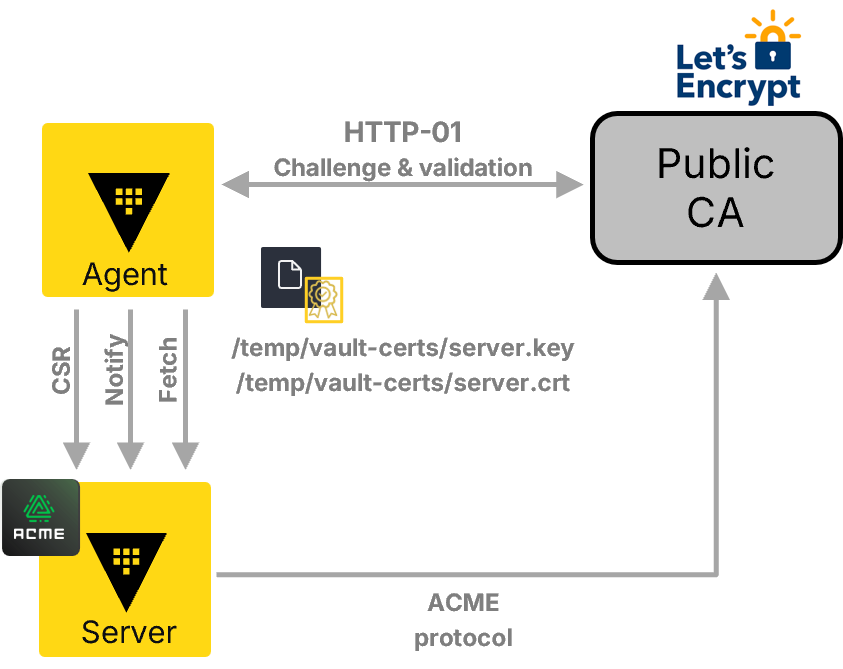
The integration employs the Automated Certificate Management Environment (ACME) protocol, which provides a vendor-agnostic interface for orchestrating public CAs. Here’s how it functions:
Native Integration with Leading CAs
Vault now supports direct integration with several prominent public certificate authorities, enabling organizations to centralize credentials and automate workflows for:
- Let’s Encrypt
- DigiCert
- GlobalSign (beta)
- Sectigo (beta)
Orchestration via Vault Agent
The updated Vault agent serves as the primary orchestrator between Vault and public CAs. It handles domain validation challenges efficiently. In this initial release, support is provided for the HTTP-01 challenge, allowing Vault to automate domain ownership verification by serving specific tokens over HTTP. Future updates will include support for DNS-01 challenges, which will facilitate wildcard certificates and accommodate non-web-accessible environments.
Streamlined Workflows
This integration supports both secure Certificate Signing Request (CSR)-based workflows—where private keys remain within an organization’s infrastructure—and flexible identifier-based workflows that allow rapid issuance of certificates.
Capabilities Available Now
The new feature enables security and platform teams to perform several tasks directly within the Vault ecosystem:
- Set Up Integrations: Configure secure connections with chosen public CAs through native Vault configuration easily.
- Request and Download Certificates: Development teams can request public certificates via the Vault API, CLI (Command Line Interface), or UI (User Interface) and download them immediately upon issuance.
- Manual Renewal: Teams can maintain control by manually triggering renewals for public certificates through the Vault interface.
- Revocation: Public certificates created via Vault can be instantly revoked if there is any suspicion of compromise, ensuring up-to-date external security posture.
- Terrraform Integration: Automate setup and management of public CA integrations using the updated Terraform Vault provider.
What This Means for Enterprises
The expansion of HashiCorp Vault’s capabilities marks a significant step toward simplifying PKI management within organizations. By integrating public CA management into its ecosystem, HashiCorp eliminates much of the manual friction that has long hindered security teams. Organizations no longer have to choose between automation and maintaining public trust; they can effectively achieve both with this new functionality.
This update is particularly relevant for technical decision-makers aiming to reduce operational risks associated with outages caused by expired certificates or manual errors. It also offers practitioners a streamlined approach to managing their PKI strategy in an increasingly complex digital landscape where security is paramount.
For more information, read the original report here.