The fairly recent method is only available from a handful of providers like xnspy.com. The key benefit of a no-jailbreak version of an iOS spyware is it doesn’t bound you to access the target device physically and install the program on the phone to gather information. It works by catching the backups sent using Cupertino-based firm’s free iCloud backup service. It requires you to have the Apple ID and password of the person you wish to track. This frees you from the worry of manually installing the app on the device. However, the spying method gives limited reported compared to the regular spy software or jailbreak edition. But the main point is it actually lets you spy on an iPhone without jailbreaking.
Jailbreaking is a process of bypassing Apple’s strict built-in rules on installing programs from sources other than Appstore. A jailbreak version of a spy app requires manual installation on the target iPhone. To use this version first, you must jailbreak the iPhone. The other important thing to remember is that things keep changing – it’s more like a competition – Apple updates its OS every year, so a new jailbreak version is required to work with the new operating system. If someone has jailbroken your device, it’s nearly impossible for you to outwardly spot the difference. Unless, the person who did it was in a rush and forget to delete the
jailbreaking tool (Cydia, SBSettings, Installous or Icy) from your iPhone. Now that you have developed some understanding of jailbreaking and different OS versions, let’s delve in to see what happens when a cell phone tracking app is installed on an iPhone.
What Happens When an iOS Spyware is Installed on Your iPhone?
Once an iOS spy software is installed on your iPhone it will start recording all the activities that take place on the phone and upload them to the person URL account of the person who wants to keep a close eye on you. Here is what an iOS Spyware will record:
Monitor Text Messages: All text messages including SMSs and emails will be recorded and uploaded to an online account from where the devious person can monitor your sent and received messages. He or she can see the actual content of the messages along with time and date stamps.
Call Log Details: Every call you have made or received on your iPhone will be intercepted by the spyware as it will gather the phone numbers, contact names together with time and date stamps and forward it to the trickster who wants to get a hold of these details.
Internet Browsing History: This feature provides the list of websites visited using your iPhone’s web browser.
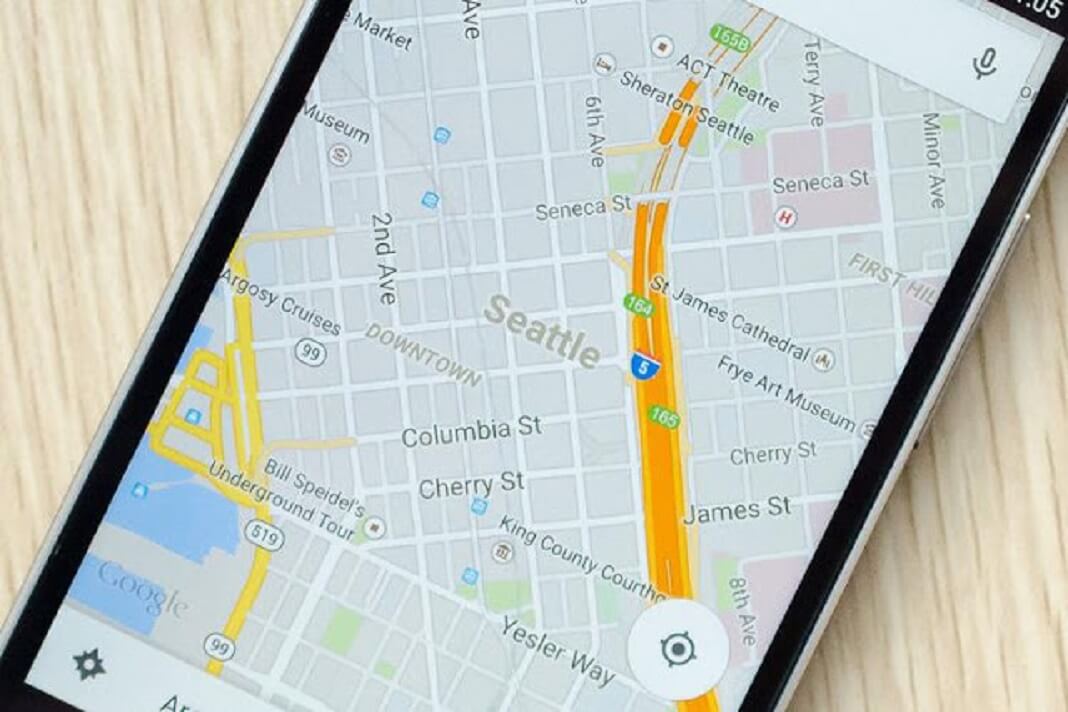
Location Tracking: It allows the sneaky person to trace your current location in real-time. The swindler can see it on a map and usually it’s very accurate.
Stored Data on the iPhone: All the images, videos, audios, and contacts saved on your smartphone can be easily accessed if a reliable spy system is tracking your device.
To your surprise, the aforementioned functionalities are considered basic features with most tracking software packages. Things can get more intense when you look at some of the advanced features offered by spy app developers at extra cost. Thanks to the fierce competition in the miniature spyware industry, software providers are trying to outdo each other by offering more advanced monitoring capabilities. Check out some of the advanced functionalities offered by modern iOS tracking apps.
Call Recording: Just as it sounds, the feature is used to record voice calls received or made by the target iOS phone. The recordings of these voice calls can be used against you if you are found guilty of a serious offense or violation.
Surround Recording: This feature allows the double-dealer to turn on the microphone on your device and record everything you can hear.
Track IM Chats: Popular instant messaging platforms like iMessage, Facebook Messenger, WhatsApp, Viber, Line, etc. that you are using to connect with your friends and family members would also be under surveillance.
Remote Controlling: A sophisticated monitoring app also lets the perpetrator remotely control your target smartphone. This is a very powerful feature as the trickster can use it to lock or wipe the data from your iPhone.
Trigger Alerts: A cheater can easily set up specific trigger words, names, numbers, email addresses or locations which when flagged up will instantly notify him or her about a certain activity.
To sum up, a tracking software can seriously interrupt your privacy and reveal all the secrets of your heart. So never share your phone or Apple details with anyone.









































What actually is a remote feature? By remotely controlling a phone do you mean we can control its movement, calls or any other specific feature? What can it do for monitoring? Can we remotely lock the phone or deny access to a particular app while using this app?
And what about the price of the app? How much for all these features? Is there any difference in price between its Jailbreak or No-Jailbreak version? Do they offer any trial version if we want to check the app? Please guide me about my queries!