PowerShell has an execution policy that acts as a safety measure to regulate the conditions for loading configuration files and running scripts. This helps prevent malicious scripts from executing. Execution policies dictate if you can load configuration files like your PowerShell profile. And if scripts need digitally signed before running. You are able to set an execution policy for the local computer system, the current user, or a particular session on a Windows PC.
So, what happens when you try to run a script on PowerShell?
When you try to run a script on PowerShell, the execution policy that remains currently set will determine if the script can run. If the script meets the requirements of the current execution policy, it will execute. If it does not meet the needs of the current execution policy, an error message will display stating that running scripts disable on this system.
For example, if your current execution policy only allows signed scripts to run and you try to run an unsigned script, you will receive an error message stating that running scripts remain “disabled” on this system.
So, if you are looking to run scripts on your Windows 11, then you need to set a different execution policy. There are several execution policies that you can set to run scripts. Let’s learn more about executions policies so that way you get an idea of which one to change into.
Also Read- Steps For Backup And Restore Quick Settings In Windows 11
What are Execution Policies and how many of them exist?
Execution policies in PowerShell determine whether you can load configuration files or run scripts and whether scripts must be digitally signed before they are run. The default scope for the Set-ExecutionPolicy cmdlet is LocalMachine, which affects everyone who uses the computer.
It’s crucial to note that execution policies are not a security measure. They can be easily bypassed and are intended more as primary rules to prevent you from unintentionally violating the policies. In other words, execution policies are there to help you avoid running scripts or configurations that could potentially harm your system without realizing it.
Let’s say you have a script called “myscript.ps1” that you want to run on your computer. If your execution policy designates to Restricted (the default), you won’t be capable to run the script at all.
If your execution policy is specified to AllSigned, you will solely be able to run the script if signed by a trusted publisher.
Also Read- How To See Seconds For Windows 11 Clock
There are six execution policies of PowerShell, let’s discuss each one of them so you get a better understanding of each type.
1. Restricted Policy
All Windows 11 PCs generally assign the Restricted policy, which is the most strict one. Running PowerShell scripts, configuration files, or module script files is not permitted thus only individual commands could be executed.
2. Unrestricted Policy
Unsigned scripts can run by default on non-Windows computers and this policy cannot be modified. There is a chance that dangerous scripts will run as a result. Before executing scripts and configuration files that don’t belong to the local network zone, the user gets forewarned.
Also Read- How To See List Of Available Restore Points In Windows 11
3. AllSigned Policy
Only signed PowerShell scripts could execute under the All Signed execution policy. This includes any unique scripts you create. You will have the option to choose whether to trust or distrust the publisher of the script if not classified.
4. Remote Signed Policy
Scripts can run on Windows server systems thanks to the default execution policy. Scripts and configuration files obtained via the web need to have a trustworthy publisher’s digital signature. Digital signatures are not necessary for locally created scripts that are not downloaded from the internet. If unblocked with the “Unblock-File cmdlet”, scripts that obtain from the internet but remain un-signed can still execute. Running harmful signed and unsigned scripts from sources other than the internet is a risk associated with this policy.
Also Read- You Can Now Run Windows 11 On An Apple Silicon Mac
5. Undefined Policy
If the current scope does not specify an execution policy. And the execution policy in all scopes is Undefined. Then the effective execution policy will Restrict for Windows clients and RemoteSigned for Windows Server. This means that if no specific execution policy has been set, Windows clients will default to the most restrictive policy while Windows Server will default to a less restrictive policy that still requires scripts downloaded from the internet to be signed by a trusted publisher.
6. Bypass Policy
It allows all scripts to run without any cautions or prompts. This type of policy intends to benefit in specific scenarios where a script is part of a larger application. Or where PowerShell itself utilize as the foundation for a program along with security measures in place.
Moreover, to control which scripts allow to run on your system, execution policies can establish at various scopes. MachinePolicy, UserPolicy, Process, CurrentUser, and LocalMachine are the available scopes.
- MachinePolicy: This scope defines by a Group Policy for all users of the computer.
- UserPolicy: This scope describes a Group Policy for the current user of the PC.
- Process: This scope only affects the current PowerShell process.
- CurrentUser: This scope only affects the current user of the computer.
- LocalMachine: This scope affects all users of the computer. (set by default when assigning the execution policy)
You can specify the scope when setting an execution policy using the -Scope parameter with the Set-ExecutionPolicy cmdlet. For example, to set an execution policy for only the current user, you would use:
Set-ExecutionPolicy -Scope CurrentUser -ExecutionPolicy RemoteSigned
Now you know all about the execution policies and the particular scopes. Let’s move on to how you can change the PowerShell Script Execution Policy in Windows 11
Also Read- How To Download Fonts For All Languages In Windows 11
change the PowerShell Script Execution Policy in Windows 11
Follow the steps given below to change the Execution Policy:
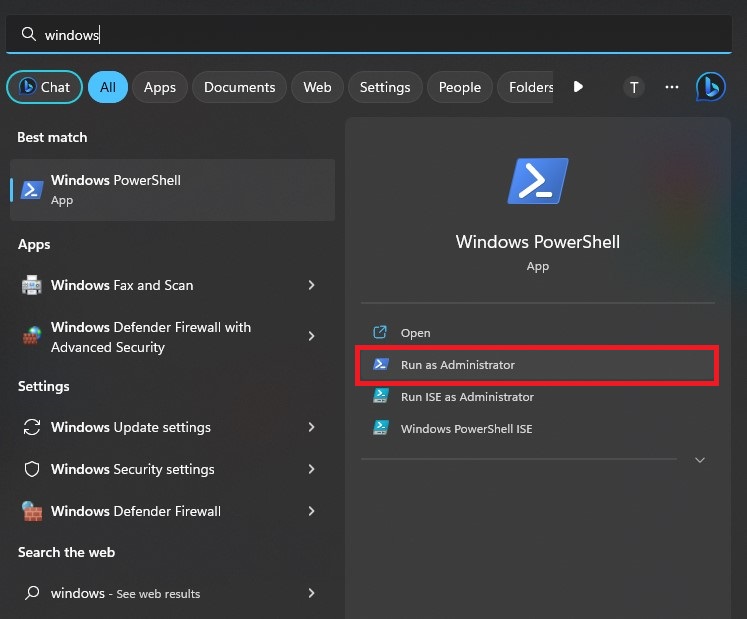
Note: If you have Windows Vista or further new versions, start PowerShell with the Run as administrator option for administrator privileges to run commands.
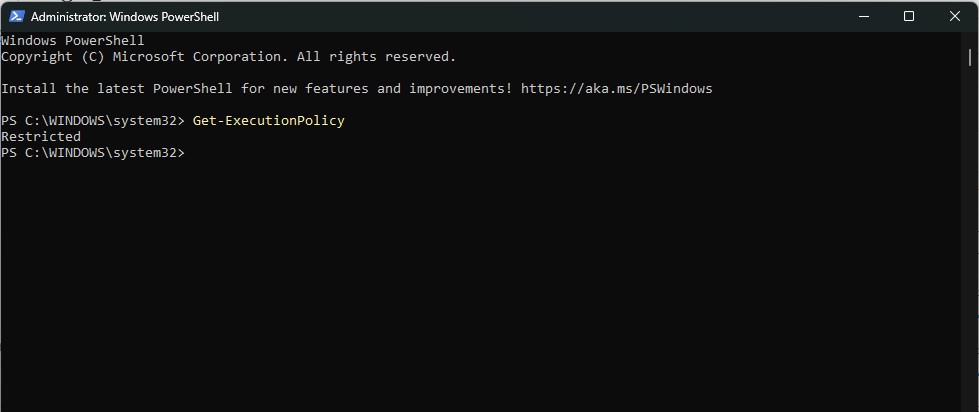
Step 1: Check your present execution policy
To do that, Jot down the following command and hit enter
Get-ExecutionPolicy
Step 2: Change the Execution Policy
to change the policy, write down the following command, and then hit enter.
Set-ExecutionPolicy RemoteSigned
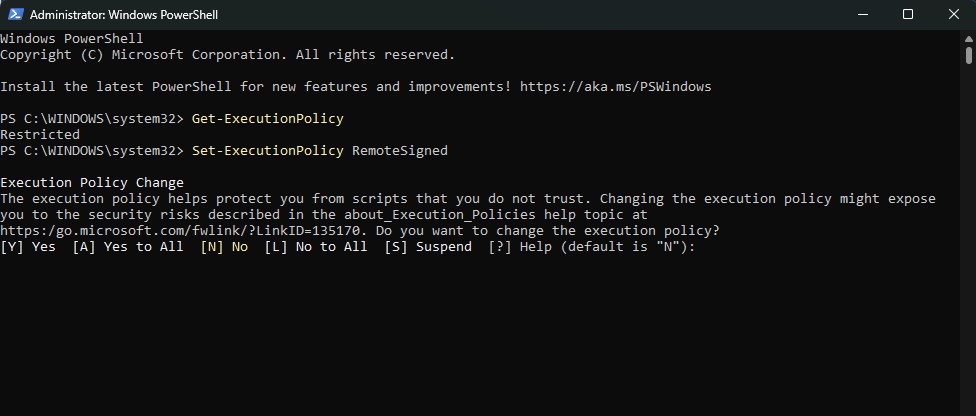
As you can see in the illustration above, you will get the Execution Policy Change notice once you hit enter.
Now that you have successfully followed the procedure. Repeat the script once again and it will begin to run on your windows 11.
For a particular Scope:
In case you want to set it for a particular scope, you can use the following command and hit enter:
Set-ExecutionPolicy -ExecutionPolicy <Policy name> -Scope <Scope name>
To Remove the Execution Policy
To remove an execution policy set for a specific scope. You can use the Set-ExecutionPolicy cmdlet with the -Scope parameter and specify Undefined as the execution policy. This removes any execution policy set for the specified scope.
For instance, to delete the execution policy for all local computer users, you can type the command like this:
Set-ExecutionPolicy -ExecutionPolicy Undefined -Scope LocalMachine
Keep in mind that when you change the execution policy for either the LocalMachine or CurrentUser scopes. The change remains stored in the registry and remains in effect until you change it again. However, if you set the execution policy for the Process scope. Thus, it remains unsaved in the registry and only lasts until the current process and any child processes close.
Also Read- How To Enable Or Disable Changing Desktop Background In Windows 11


































